Onion links, also known as .onion addresses, serve as gateways to the Tor network. That enigmatic pathways lead you to a hidden realm where anonymity reigns supreme. Within this labyrinthine world, one can find a myriad of sites that bypass traditional search engines. Proceed with caution, as the darknet harbors both benevolent communities and shadowy operations. Navigating this volatile terrain requires a keen eye for discernment and a firm grasp of online safety protocols.
- Remember to use strong passwords and multi-factor authentication for any accounts accessed through onion links.
- Employ extreme caution when downloading files or communicating with strangers on the darknet.
- Keep abreast of about the latest security threats and best practices for online privacy.
Explore the Shadows of the Internet with Tor
The darknet, a labyrinthine realm shrouded in anonymity and intrigue, beckons curious explorers. To traverse this shadowy domain, one requires unconventional onionlinks tools - primarily, onion links. These encrypted pathways, facilitated by the Tor network, provide access to hidden services, where anythinggoes. A deep dive into the darknet with onion links promises a glimpse into a world of controversy, but it's a journey fraught with challenges.
- Navigating the onion link landscape requires awareness.
- Threats lurk around every corner, poised to compromise your assets.
- Moral dilemmas abound as you encounterprohibited content.
This exploration demands carefulness. Proceed with caution, for the darknet is a place where truthcan be twisted.
Navigating the Labyrinth: A Guide to Onion Links
Diving deep into the digital realm often requires solving layers of mystery. Onion links, like their namesake vegetable, hide their true nature beneath multiple levels. These encrypted pathways direct to information that might otherwise be unavailable. To master this labyrinth, you'll need a set of key skills and a sharp mind.
- {Firstly|First|, it's essential to understand the structure of an onion link. Each layer acts as a stepping stone, routing you closer to the final destination.
- {Secondly|Next|, familiarize yourself with the tools required to reveal these links.
- {Lastly|Finally|, remember that navigating onion links requires a robust internet connection.
Exercise discretion when exploring the depths of onion links, as not all data is legitimate.
Protected Communication Through Onion Links
Onion links offer a robust method for ensuring secure communication. This method relies on multiple layers of encryption, much like the structure of an onion. Each layer is responsible of scrambling the data, making it highly impossible for unauthorized users to decode the information. This complex approach creates a protected tunnel for your data, ensuring that only the intended recipient can unveil the true message.
- Furthermore, onion links improve privacy by masking the sender's and receiver's IP addresses.
- Consequently, they are commonly used for sensitive communication, such as whistleblowing, political activism, and news gathering in areas with censored internet access.
Exploring the Underbelly: Onion Link Destinations
Diving deep into the shadowy recesses of the web can be a thrilling experience. Onion link destinations, shrouded in layers of encryption, often lead to forbidden territories where the secrets are exposed. Whether you're a curious explorer seeking knowledge or a investigator navigating the volatile world of cyberspace, onion links offer a passage to an parallel reality.
- Discovering the truths behind the curtain.
- Communicating with individuals who demand anonymity.
- Utilizing platforms designed for secretive activities.
Unmasking the Secrets of Anonymity: A Look at Onion Links
Onion links are like enigmatic passages on the web, leading to sites that are shrouded in obscurity. These networks, often referred to as the deep web, operate under layers of security that make them nearly impossible to trace. This cloak of secrecy allows users to browse the internet with a high degree of confidentiality.
- Accessing these onion sites requires special tools like The Onion Router.
- After accessing, you can explore a vast and extensive range of content, from blogs and chat rooms to illegal marketplaces.
- Keep in mind, the anonymity offered by onion links can also be used for malicious purposes.
The power of anonymity afforded by onion links is a double-edged sword, offering both opportunity and potential for abuse.
 Jennifer Grey Then & Now!
Jennifer Grey Then & Now!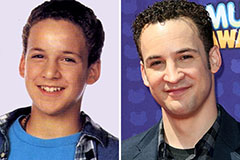 Ben Savage Then & Now!
Ben Savage Then & Now! Tiffany Trump Then & Now!
Tiffany Trump Then & Now! Barbi Benton Then & Now!
Barbi Benton Then & Now!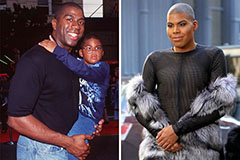 Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now!